Execution safety and auditability without rewriting your stack.
The Three Seals.

Seal 01
Idempotency Gatekeeper

No action should happen twice by accident.
Axnith enforces replay-safe behavior under retries, partial failures, and uncertain delivery conditions.
Seal 02
Sealed Proof

Proof, not generic logs.
Axnith seals identity, policy result, reason codes, and evidence references into audit-grade proof surfaces designed for governance, review, and accountability.
Seal 03
Risk Guard

Unsafe actions are blocked or held before they spread harm.
Axnith contains risk through policy, thresholds, and SAFE_HOLD semantics while preserving operational continuity where possible.
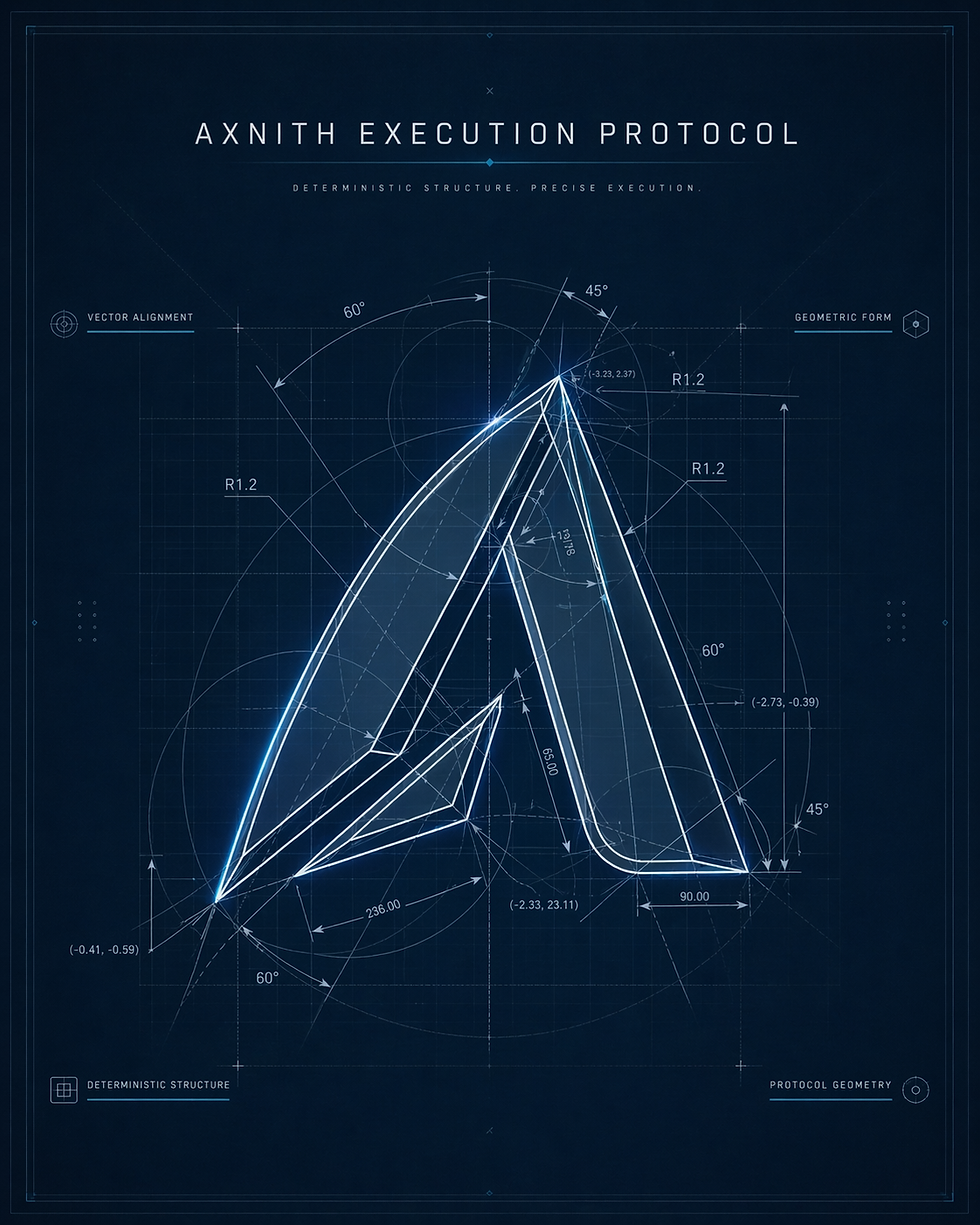
The Deterministic Lifecycle

The Seals define the promise.
The Deterministic Lifecycle shows how Axnith keeps it.
PRECHECK → Validate policy, bounds, readiness, and execution discipline before side effects begin.
APPLY → Perform the intended change through the relevant
execution surface.
VERIFY → Confirm what actually happened in the real system.When reality cannot
yet be verified, Axnith models uncertainty honestly instead of pretending certainty.
FINALIZE → Seal the outcome into proof: intent identity, lifecycle result, reason codes, and evidence references.
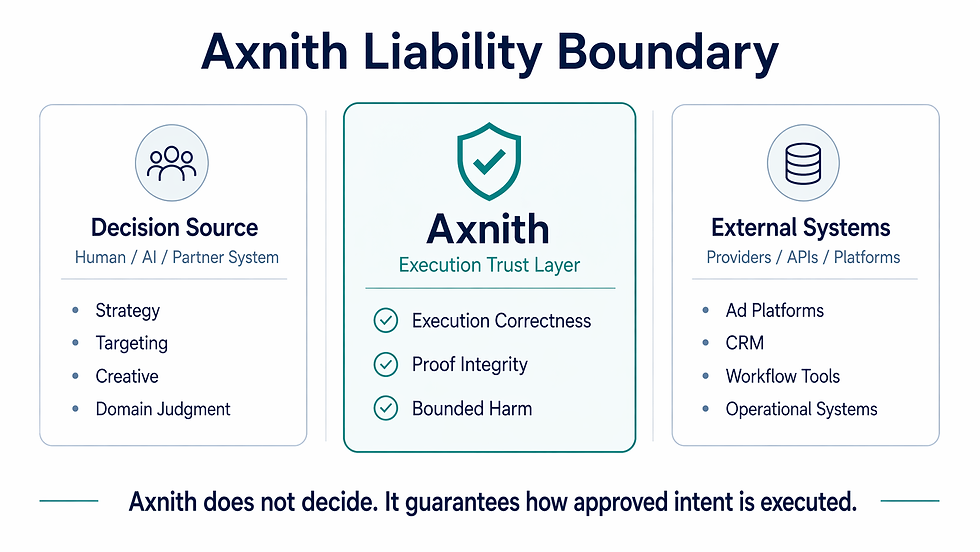
Why this matters
The trust gap lives in the last mile.
Modern systems already have observers and recommenders. The real risk begins when intent becomes execution.Retries, race conditions, partial failures, policy drift, and unverifiable outcomes create operational anxiety exactly at that boundary.Axnith closes that gap by making execution deterministic, policy-governed, replay-safe, proof-backed, and bounded in harm.